Radio Frequency Identification 1
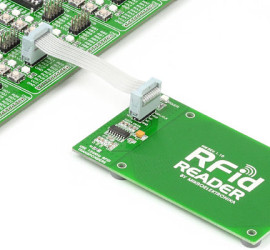
RFID stands for ‘Radio Frequency Identification’. It is short range communication system. An RFID consist of three main parts an antenna, transponder and a receiver. It is used to transfer data and is transferred through electromagnetic and electrostatic coupling. Data size can range from 2000 bytes and less. RFID system uses tag for identification of object. It consists of radio frequency transmitter and receiver. These tags contains unique tag serial […]